How to Use GitHub Actions Automated Deployments for Modern Software
Introduction
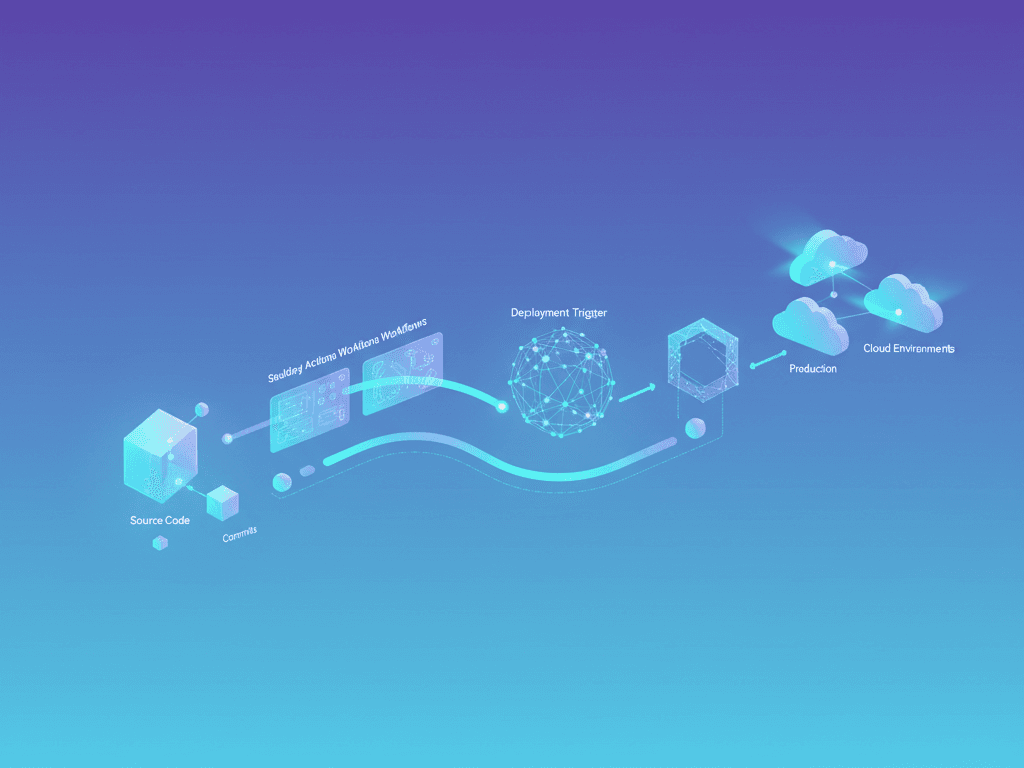
Modern software development demands speed and reliability. Most New Zealand businesses now face intense pressure to release features faster than ever. Consequently, manual deployment processes have become a significant bottleneck. They often lead to human errors and inconsistent environments. This is where GitHub Actions enters the frame as a transformative solution. This platform allows you to automate your entire software development workflow directly within your repository. You can build, test, and deploy code without leaving the GitHub ecosystem. It offers a seamless bridge between your source code and your production servers. By learning how to use GitHub Actions automated systems, you ensure your team remains competitive. We will explore the technical nuances and strategic advantages of this tool. This guide aims to help Kiwi developers and business owners achieve deployment excellence through automation and modern DevOps practices.
The Foundation
Before diving into the code, you must understand the core components of GitHub Actions. At its heart, the system relies on workflows. These are automated processes that you define in YAML files. Every workflow contains one or more jobs. These jobs run on specific runners, which are virtual machines or containers. GitHub provides hosted runners for various operating systems like Linux, Windows, and macOS. Within these jobs, you define steps. Each step represents an individual task, such as running a script or an action. Actions are the smallest building blocks. They are reusable units of code that perform common tasks. For instance, you might use an action to check out your repository. Another action could set up a specific programming language environment. Understanding these hierarchies is essential for building robust pipelines. This foundation ensures your automation logic remains modular and easy to maintain over time.
Architecture & Strategy
Strategic planning is vital before you implement any automation. You must align your deployment architecture with your current tech stack. Many organisations in New Zealand prefer AWS, Azure, or Google Cloud for hosting. Your GitHub Actions workflow should integrate deeply with these providers. Consider using a branching strategy like GitFlow or Trunk-based development. These strategies dictate when a workflow should trigger. For example, you might run tests on every pull request. However, you only trigger a production deployment when code merges into the main branch. You should also consider using environments within GitHub. This feature allows you to set protection rules and required reviewers for sensitive deployments. This architecture provides a clear path from local development to a live environment. It minimises risks and ensures that only high-quality, verified code reaches your end users in New Zealand and beyond.
Configuration & Tooling
Setting up your environment requires the right tools and configuration. You primarily interact with GitHub Actions through the .github/workflows directory. This directory resides at the root of your project. You will need a capable code editor like VS Code. Many developers use the GitHub Actions extension to validate their YAML syntax in real-time. Managing secrets is another critical step. Never hardcode API keys or passwords in your workflow files. Instead, use GitHub’s encrypted secrets feature to store sensitive data securely. You can then reference these secrets in your workflow using a specific syntax. Additionally, consider using third-party tools like Docker for consistent build environments. Tools like Terraform or Pulumi can also work alongside GitHub Actions. They help manage your infrastructure as code alongside your application logic. This holistic approach to tooling creates a professional and scalable deployment ecosystem.
Use GitHub Actions Automated Development & Customisation
Let us create a practical deployment workflow. This example demonstrates how to deploy a static website or a simple application. First, you create a file named deploy.yml in your workflows folder. You must define the trigger, such as a push to the main branch. Next, you specify the runner and the sequential steps. Here is a basic code snippet to get you started:
name: Production Deployment
on:
push:
branches: [ main ]
jobs:
deploy:
runs-on: ubuntu-latest
steps:
- name: Checkout Code
uses: actions/checkout@v3
- name: Set up Node.js
uses: actions/setup-node@v3
with:
node-version: '18'
- name: Install Dependencies
run: npm install
- name: Build Project
run: npm run build
- name: Deploy to Server
run: echo "Deploying to production server..."This script ensures that every push to the main branch triggers a fresh build. You can customise the deployment step to use Rsync, SSH, or cloud-specific CLI tools. This modularity allows you to adapt the workflow to any hosting provider. By following this structure, you create a repeatable and reliable deployment cycle.
Advanced Techniques & Performance Tuning
Performance optimisation is crucial for maintaining a fast development loop. Long build times frustrate developers and delay critical updates. You can use caching to significantly speed up your workflows. GitHub provides a dedicated action to cache dependencies like npm modules or Maven packages. This prevents the runner from downloading the same files repeatedly. Furthermore, consider using parallel jobs. If your test suite is large, split it across multiple runners. This reduces the total execution time of the workflow. You can also use matrix builds to test your application across different versions of a language or operating system. Here is an example of a matrix configuration:
strategy:
matrix:
node-version: [14.x, 16.x, 18.x]
os: [ubuntu-latest, windows-latest]This configuration runs your tests in six different environments simultaneously. For New Zealand companies with international users, this level of verification is invaluable. It ensures broad compatibility and high performance across various platforms.
Common Pitfalls & Troubleshooting
Even expert developers encounter issues when they use GitHub Actions automated workflows. One common mistake is misconfiguring permissions. The default GITHUB_TOKEN might lack the necessary scopes to write to the repository or access specific APIs. Always check your workflow permissions settings in the repository configuration. Another frequent issue involves environment variables. Ensure you are using the correct naming conventions and that secrets are correctly scoped to the environment. If a workflow fails, examine the logs carefully. You can enable debug logging by setting a secret named ACTIONS_STEP_DEBUG to true. This provides much more detailed output for every step. Remember that network issues can sometimes occur during external API calls. Implement retries for critical steps to make your pipeline more resilient. Regularly auditing your workflow logs helps identify recurring patterns and prevents future failures.
Real-World Use GitHub Actions Automated Success
Consider a hypothetical New Zealand startup called “KiwiTech Solutions.” They originally deployed their web application manually using FTP. This process took nearly forty minutes and often caused downtime. After they learned how to use GitHub Actions automated deployments, their productivity soared. They integrated automated unit tests and security scans into their pipeline. Now, their deployments take less than five minutes. They also achieved a zero-downtime deployment model using blue-green deployment strategies. This change allowed their developers to focus on writing code rather than managing releases. From a business perspective, they reduced operational costs and improved customer satisfaction. The ROI was immediate and substantial. This success story reflects the experiences of many modern Kiwi enterprises. They leverage automation to punch above their weight on the global stage. GitHub Actions provides the professional-grade infrastructure needed for such scaling.
Future Outlook & Trends
The world of CI/CD is evolving rapidly. We expect to see deeper integration of Artificial Intelligence within GitHub Actions. AI could soon suggest workflow optimisations or automatically fix broken scripts. GitHub is also expanding its fleet management capabilities. This will allow larger organisations to manage workflows across hundreds of repositories more easily. Another trend is the rise of Software Bill of Materials (SBOM) generation. Security-conscious companies in New Zealand will use automated workflows to generate these lists for every build. This ensures compliance with international security standards. Furthermore, we see a move toward serverless runners. These offer even more scalability and cost-efficiency. Staying ahead means embracing these trends and continuously refining your automation strategies. The future of deployment is more intelligent, more secure, and almost entirely invisible to the developer.
Comparison with Other Solutions
Choosing the right tool is essential for long-term success. While GitHub Actions is excellent, other platforms exist. Here is a comparison of popular CI/CD solutions:
| Feature | GitHub Actions | GitLab CI | Jenkins | CircleCI |
|---|---|---|---|---|
| Ease of Use | High | High | Low | Medium |
| Integration | Native with GitHub | Native with GitLab | Via Plugins | Good |
| Customisation | Excellent | Excellent | Extreme | Good |
| Hosting | Cloud or Local | Cloud or Local | Self-hosted | Cloud |
GitHub Actions excels due to its deep integration with the code itself. Jenkins offers more customisation but requires significant maintenance. GitLab CI provides a similar experience but is locked to the GitLab ecosystem. For most Kiwi developers already on GitHub, Actions is the most logical and efficient choice.
Use GitHub Actions Automated Checklist
Following best practices ensures your pipeline remains stable and secure. Use this checklist for your next project:
- Verify Security: Ensure all secrets are encrypted and never exposed in logs.
- Optimise Speed: Implement caching for dependencies to reduce build times.
- Linter Integration: Run code linters before the build step to maintain quality.
- Version Your Actions: Use specific versions (e.g.,
v3) instead ofmainto avoid breaking changes. - Test Coverage: Fail the build if test coverage drops below a certain percentage.
- Documentation: Add comments to your YAML files to explain complex logic.
- NZ Compliance: Ensure your data handling within the pipeline meets local privacy laws.
Regularly reviewing this list helps maintain a high standard of DevOps excellence.
Key Takeaways
- Efficiency: Use GitHub Actions automated workflows to save time and reduce manual errors.
- Integration: Seamlessly connect your code repository with major cloud providers.
- Scalability: Leverage runners and matrix builds to handle complex testing scenarios.
- Security: Protect sensitive data using GitHub Secrets and environment-specific rules.
- Cost-Effective: Reduce infrastructure management overhead by using hosted runners.
- Kiwi Context: Improve deployment reliability for New Zealand businesses regardless of size.
Conclusion
Mastering how to use GitHub Actions automated deployments is a vital skill for any modern developer. It moves your workflow from manual, error-prone tasks to a streamlined, professional pipeline. We have explored everything from basic YAML syntax to advanced performance tuning. By implementing these strategies, you empower your team to deliver value faster. You also build a more resilient and secure software delivery process. At Spiral Compute, we believe that automation is the cornerstone of successful digital transformation in New Zealand. Start small by automating your test suite. Gradually expand your workflows to handle full-scale production deployments. The benefits in terms of time, cost, and peace of mind are immense. Now is the perfect time to embrace the power of GitHub Actions. Take the first step today and transform how you build and release software.